how endbugflow software can be protected – Complete Guide to Security, Risk Management, and Best Practices
In today’s interconnected digital economy, software platforms sit at the center of business operations, customer trust, and competitive advantage. As applications become more complex and interconnected, the risks surrounding them grow just as quickly. Security is no longer a one-time setup or a checklist item; it is an ongoing discipline that blends technology, process, and people. Organizations that rely on sophisticated platforms must understand not only what threats exist, but also how to design systems that can withstand them over time. Within this context, how endbugflow software can be protected is a strategic question that touches every stage of the software lifecycle, from ideation to retirement. Addressing this question requires a structured, holistic approach rather than isolated technical fixes.
Understanding the Modern Threat Landscape
To build meaningful protection, one must first understand the environment in which software operates. Threats today are not limited to lone attackers exploiting simple weaknesses. Instead, they include organized cybercrime groups, automated attack tools, insider risks, and accidental failures caused by human error. Attack vectors range from application-layer vulnerabilities and misconfigurations to supply chain compromises and social engineering. This evolving landscape means that defensive strategies must be adaptive. When teams analyze how endbugflow software can be protected, they must account for both known risks and emerging threats that may not yet be fully understood. Proactive threat modeling and continuous risk assessment become essential foundations for any robust security program.
Security as a Design Principle, Not an Afterthought
One of the most important shifts in modern software engineering is the recognition that security must be embedded from the very beginning. Designing systems with protection in mind reduces long-term costs and prevents structural weaknesses that are difficult to fix later. This involves defining security requirements alongside functional requirements and ensuring that architectural decisions support isolation, least privilege, and fault tolerance. When considering how endbugflow software can be protected, teams should treat security as a core quality attribute, similar to performance or reliability. By doing so, they avoid the common pitfall of bolting on controls after deployment, which often leads to gaps and inconsistencies.
Secure Development Lifecycle Practices
A secure development lifecycle integrates security activities into every phase of software creation. This includes secure coding standards, automated code analysis, dependency management, and regular peer reviews. Developers should be trained to recognize common vulnerability patterns and to use frameworks and libraries responsibly. Automated testing tools can identify issues early, while manual reviews provide contextual understanding that tools may miss. From this perspective, how endbugflow software can be protected is closely tied to developer discipline and organizational culture. When security checks are part of everyday workflows, vulnerabilities are less likely to reach production environments. how to update endbugflow software on pc
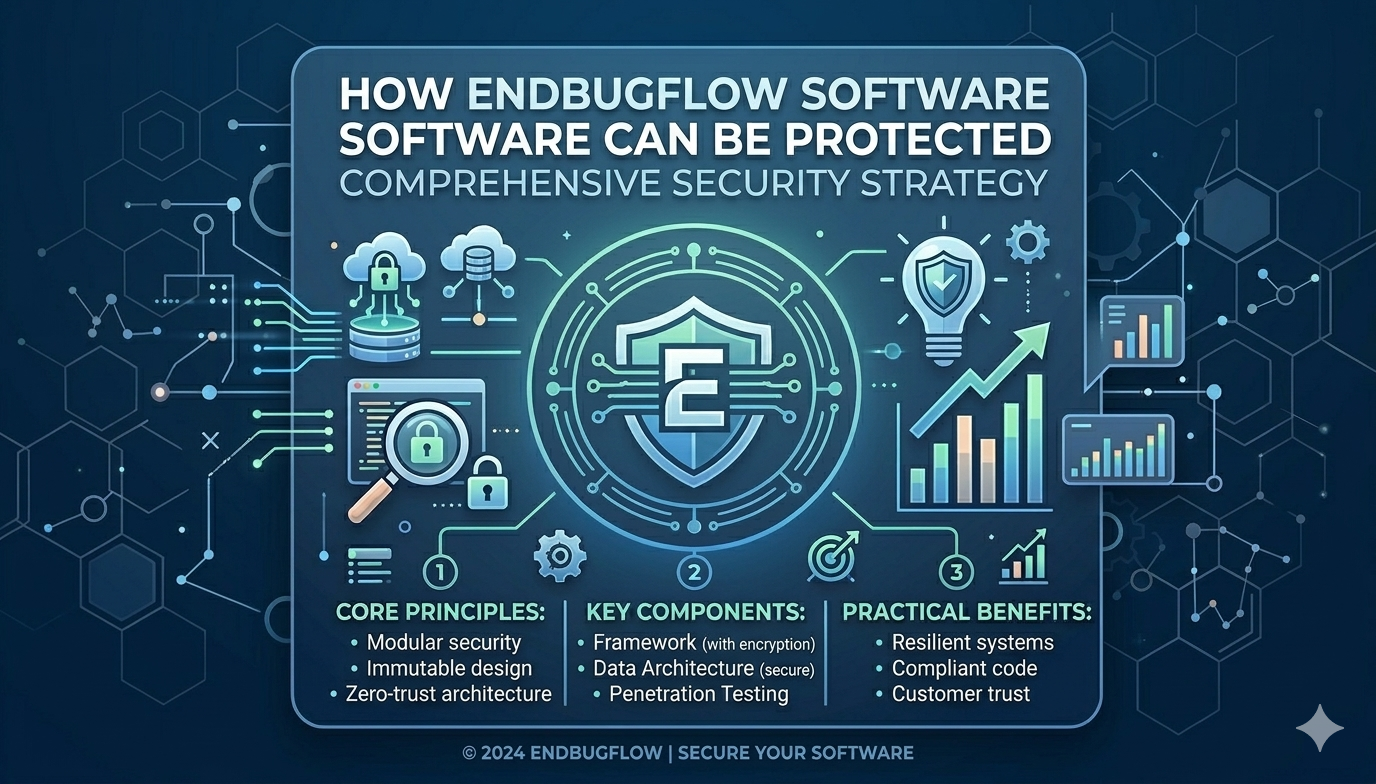
Architectural Strategies for Resilience
Software architecture plays a decisive role in limiting the impact of attacks. Modular designs, clear boundaries between components, and well-defined interfaces reduce the blast radius of failures. Techniques such as segmentation and isolation prevent attackers from moving laterally within systems. Redundancy and graceful degradation ensure that services remain available even when parts of the system are under stress. Evaluating how endbugflow software can be protected at the architectural level encourages teams to think beyond individual features and to focus on system-wide resilience. Strong architecture turns potential single points of failure into manageable risks.
Identity, Authentication, and Access Control
Controlling who can access what is fundamental to software security. Strong identity management ensures that users and services are properly authenticated, while authorization mechanisms enforce precise access rights. Multi-factor authentication, role-based access control, and regular credential rotation significantly reduce the risk of unauthorized access. Additionally, service-to-service communication should be authenticated and encrypted to prevent impersonation. In discussions about how endbugflow software can be protected, access control often emerges as one of the most effective and cost-efficient defenses. Properly implemented, it limits the damage that compromised accounts or credentials can cause.
Data Protection and Privacy Considerations
Data is often the most valuable asset within a software system, and its protection is both a security and a trust issue. Encryption at rest and in transit safeguards information from interception and unauthorized disclosure. Data classification helps teams apply appropriate controls based on sensitivity, while retention policies minimize the risk associated with storing unnecessary information. Privacy-by-design principles ensure that personal data is handled responsibly and transparently. When organizations explore how endbugflow software can be protected, they must consider not only technical safeguards but also ethical and legal responsibilities associated with data stewardship.
Infrastructure and Environment Hardening
The security of software is inseparable from the security of the infrastructure it runs on. This includes servers, networks, containers, and cloud resources. Regular patching, secure configurations, and vulnerability scanning reduce exposure to known exploits. Network segmentation and firewalls add layers of defense, while infrastructure-as-code practices promote consistency and auditability. Thinking about how endbugflow software can be protected at the infrastructure level highlights the importance of collaboration between development and operations teams. A well-hardened environment supports application security rather than undermining it.
Monitoring, Logging, and Detection
Even the best preventive measures cannot guarantee absolute protection. Continuous monitoring and comprehensive logging are therefore essential for detecting suspicious activity and responding quickly. Logs should capture meaningful events without overwhelming teams with noise, and they should be protected from tampering. Behavioral analytics and anomaly detection can identify subtle signs of compromise that traditional alerts might miss. In the broader conversation about how endbugflow software can be protected, monitoring serves as the bridge between prevention and response. It transforms security from a static posture into a dynamic capability.
Incident Response and Recovery Planning
Preparation for security incidents is a hallmark of mature organizations. Incident response plans define roles, communication channels, and decision-making processes before a crisis occurs. Regular simulations and drills help teams practice these procedures and identify gaps. Equally important is recovery planning, which ensures that systems can be restored quickly and accurately after an incident. When evaluating how endbugflow software can be protected, leaders should recognize that resilience includes the ability to recover, not just to resist. Effective response minimizes downtime, financial loss, and reputational damage.
Compliance, Governance, and Risk Management
Regulatory requirements and industry standards influence how software systems are designed and operated. Compliance frameworks provide structured guidance on controls, documentation, and oversight. However, compliance alone does not guarantee security; it must be integrated with broader risk management practices. Governance structures clarify accountability and ensure that security decisions align with business objectives. In regulated environments such as those operating in the United States, understanding how endbugflow software can be protected also involves navigating legal obligations and demonstrating due diligence. Balanced governance supports both innovation and protection.
Human Factors and Organizational Culture
Technology alone cannot secure software systems. Human behavior, awareness, and incentives play a critical role in either strengthening or weakening defenses. Training programs, clear policies, and leadership support foster a culture where security is valued rather than seen as an obstacle. Encouraging responsible disclosure and learning from mistakes promotes continuous improvement. From this human-centered perspective, how endbugflow software can be protected depends on aligning individual actions with organizational goals. A strong security culture amplifies the effectiveness of technical controls.
Continuous Improvement and Adaptation
Security is not a destination but a journey. As threats evolve and technologies change, protection strategies must be revisited and refined. Regular assessments, feedback loops, and metrics help organizations measure progress and identify areas for enhancement. Collaboration with external partners, such as auditors or industry peers, can provide fresh insights. When organizations treat how endbugflow software can be protected as an ongoing question rather than a one-time project, they position themselves to adapt effectively to future challenges. Continuous improvement ensures that defenses remain relevant and robust.

Conclusion
Protecting complex software systems requires more than isolated tools or reactive fixes. It demands a comprehensive strategy that integrates design principles, development practices, operational controls, and human awareness. By examining architecture, data handling, infrastructure, monitoring, and culture, organizations can build layered defenses that address both current and emerging risks. Ultimately, how endbugflow software can be protected is a reflection of organizational maturity and commitment. Those who invest in thoughtful, holistic protection not only reduce risk but also build trust, resilience, and long-term value in an increasingly uncertain digital world.